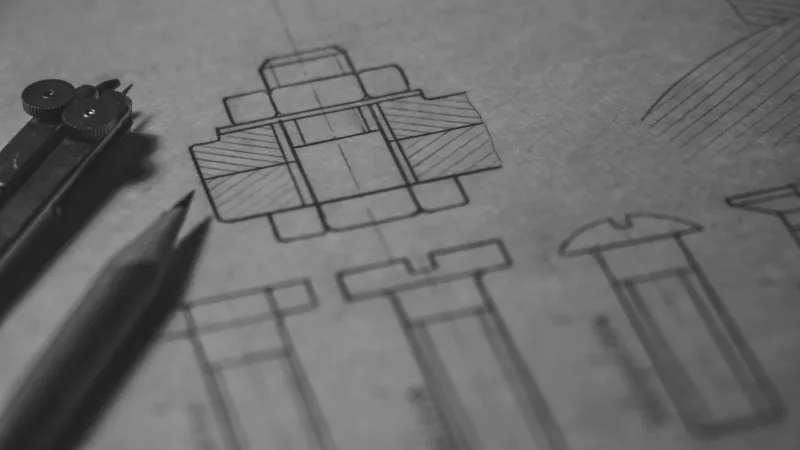
Tec(h)tonic
Insights into building a solid I.T. foundation in the mid-size business world.
-

Scripting a dynamic IP address change notifier
CONTINUE READING: Scripting a dynamic IP address change notifierThis blog is hosted on a small, Ubuntu Linux-based server in my home. Given that we have a typical, residential Internet connection, our router’s IP address is subject to change at any time (this can make it challenging to provide you, the reader, reliable access to blog.chrisjscott.net). My domain was, until recently, managed by Google’s…
-

How Do AI Neural Networks Function?
CONTINUE READING: How Do AI Neural Networks Function?A quick-hit explanation of how neural networks make decisions.
-
Lessons Learned
CONTINUE READING: Lessons LearnedReflections and learnings from my four years working for the Global Operations team of an international design firm.